The federal indictment of 26-year-old Shawn O’Brien for the interstate transmission of threats against Alexis Wilkins, partner of former Pentagon official Kash Patel, functions as a case study in the escalating friction between digital anonymity and the legal threshold of "true threats." While media narratives often frame such events as isolated outbursts of political vitriol, a structural analysis reveals a repeatable pattern of behavioral escalation, digital vulnerability, and the specific application of 18 U.S.C. § 875(c). This incident is not merely a social media skirmish; it is a data point in the shifting risk profile for public figures and their immediate domestic circles.
The Architecture of the Threat Vector
Targeted harassment in the contemporary political environment operates through a three-stage lifecycle: identification, provocation, and transmission. In the O’Brien case, the identification phase bypassed the primary political actor—Kash Patel—to focus on a secondary target, Alexis Wilkins. This strategy, known as "networked harassment," aims to maximize psychological impact by targeting individuals who lack the state-sponsored security apparatus often afforded to high-ranking officials.
The provocation in this instance was centered on a series of direct messages sent via Instagram. The specific phrasing cited in the Department of Justice filings—"watch your back"—transcends protected political speech by establishing a credible apprehension of physical violence. Legally, the distinction rests on the objective-person standard: would a reasonable person find the communication to be a serious expression of an intent to commit an act of unlawful violence?
The transmission mechanism utilized was Instagram’s Direct Message (DM) platform. This choice of medium provides a false sense of privacy for the perpetrator while ensuring the high-impact delivery of the threat directly to the target’s personal device. The jurisdictional trigger for federal involvement stems from the interstate nature of the communication; O’Brien, located in Massachusetts, transmitted data across state lines to reach Wilkins, thereby activating federal statutes.
The Legal Cost Function of Digital Intimidation
The prosecution of O’Brien utilizes 18 U.S.C. § 875(c), which carries a maximum penalty of five years in prison, three years of supervised release, and a fine up to $250,000. To understand the gravity of these charges, one must analyze the "Cost Function" of such actions. The legal system seeks to set the price of political intimidation high enough to deter the "lone wolf" actor who perceives their digital actions as cost-free.
- The Evidentiary Trail: Digital threats leave a forensic footprint that is nearly impossible to erase. Metadata including IP addresses, device IDs, and timestamps provide a roadmap for federal investigators.
- Intent vs. Capability: Under current legal frameworks, the government does not necessarily need to prove that O’Brien had the immediate physical capability or a logistical plan to carry out the threat. The crime is the transmission of the threat itself.
- The Deterrence Multiplier: By pursuing these cases at the federal level, the Department of Justice signals that geographical distance provides no shield. The cost of a "heat-of-the-moment" message can result in a lifetime of felony-related civil disabilities.
The Vulnerability of Secondary Targets
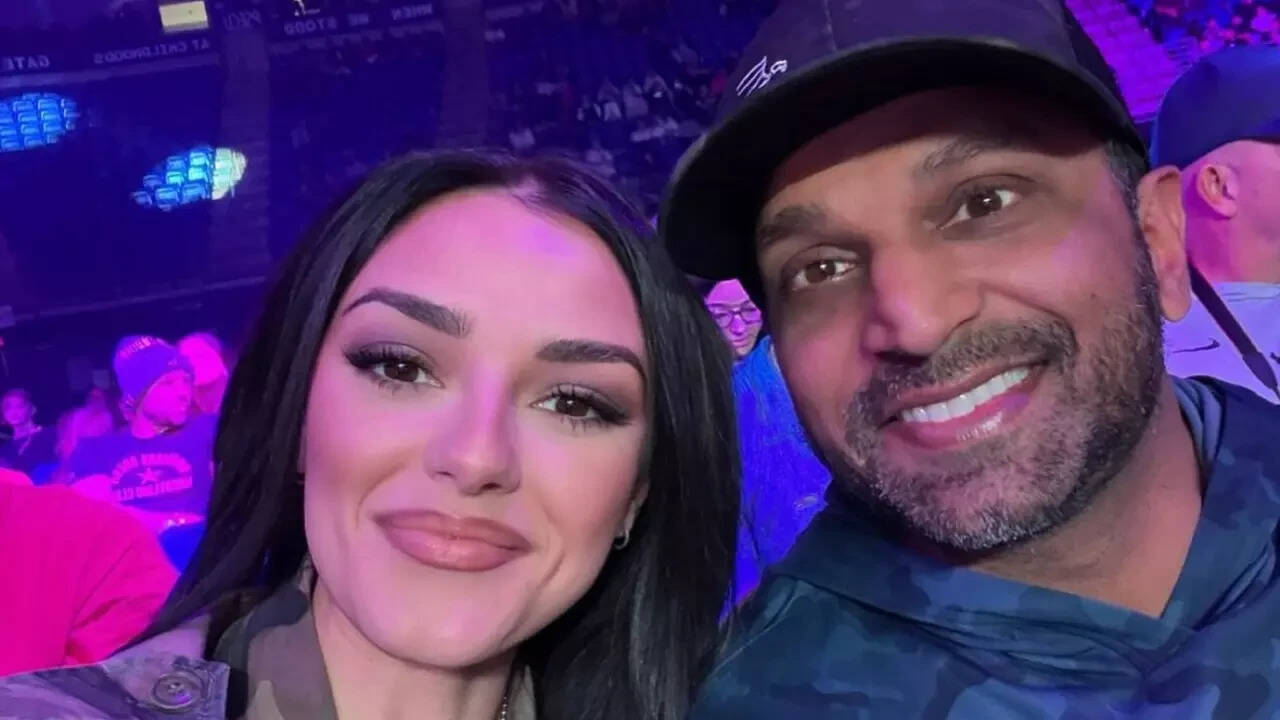
The targeting of Alexis Wilkins highlights a critical flaw in the security posture of many public figures. High-profile individuals often harden their own digital and physical footprints, yet their associates—partners, children, or employees—frequently remain "soft targets."
The psychological logic of the harasser suggests that striking a loved one yields a higher "distress ROI" (Return on Investment) than shouting into the void of a public figure’s mentions. For Wilkins, a singer and public personality in her own right, the threat vector is widened by her professional necessity to maintain an open digital presence. This creates a paradox: the need for public engagement facilitates the access required for harassment.
Operational Failures in Perceived Anonymity
Shawn O’Brien’s arrest by the FBI’s Joint Terrorism Task Force (JTTF) underscores a fundamental misunderstanding of digital privacy. Many individuals operating in the political fringe believe that social media platforms protect their identity from law enforcement. The reality is a streamlined process of subpoenas and warrants:
- Subpoena of Platform Data: Federal agencies routinely obtain subscriber information from Meta (Instagram’s parent company).
- Geographical Triangulation: Even if a user employs a VPN, secondary data points—such as the timing of logins or associated recovery emails—often lead back to a physical identity.
- Physical Evidence Recovery: Upon his arrest, O’Brien’s electronic devices were subject to seizure, likely providing further evidence of premeditation or repeated patterns of behavior.
The failure to account for these forensic realities suggests a cognitive dissonance common among digital harassers. They view the internet as a consequence-free zone, failing to realize that every packet of data sent is a potential piece of evidence in a criminal trial.
The Escalation Ladder of Political Violence
Social scientists and law enforcement analysts often track what is known as the "pathway to violence." This pathway is rarely a straight line but rather a series of escalatory steps:
- Grievance Formation: A perceived political or personal wrong.
- Ideation: Thinking about using violence or threats to address the grievance.
- Research and Planning: Gathering information on the target (doxing).
- Breach: The actual transmission of the threat or physical approach.
In the O’Brien case, the transmission of the message "watch your back" represents a "Breach" of the target’s digital perimeter. The involvement of the JTTF indicates that law enforcement viewed this not as a random insult, but as a potential precursor to physical harm. The rapid intervention was designed to "off-ramp" the individual from the pathway to violence before the ideation could manifest as physical action.
Strategic Mitigation for High-Profile Domestic Units
For individuals in the orbit of high-stakes political figures, the O’Brien incident serves as a catalyst for a revised security protocol. Relying on platform moderation or "blocking" functions is insufficient when dealing with determined harassers.
The first step is the aggressive compartmentalization of personal and professional digital identities. Using alias-based hardware for personal communications and strict "no-location" policies for real-time posts are fundamental. The second step involves the pre-emptive documentation of all harassing communications. The success of the prosecution in the O’Brien case relies heavily on the integrity of the digital evidence provided by the victim.
The legal landscape is also evolving. While the First Amendment provides broad protections for "rhetorical hyperbole" or "unpleasant speech," the court’s interpretation of what constitutes a "true threat" is becoming more refined in the digital age. Perpetrators can no longer hide behind the defense of "it was just a joke" when the target is a specific individual and the language implies physical monitoring ("watch your back").
The prosecution of Shawn O’Brien serves as a mandatory corrective to the narrative that digital threats are intangible. By quantifying the legal risks and exposing the forensic vulnerability of the perpetrator, the case establishes a clear boundary: the digital transmission of fear is a measurable, punishable offense.
For those managing the security and public relations of political figures, the focus must shift from reactive blocking to proactive threat assessment. This includes monitoring for "fixated interest"—a psychological state where an individual becomes obsessively focused on a public figure or their family. Identifying these patterns early allows for law enforcement intervention before the "breach" occurs.
The strategic play here is not to withdraw from the public square, but to harden the infrastructure surrounding it. Treat every direct message as a potential court exhibit. Audit the digital footprints of all family members. Ensure that the "cost" of harassment is clearly communicated to potential actors through the visible and relentless prosecution of those who cross the line from speech to threat.