The remote worker you just hired might be building a nuclear missile. On March 12, 2026, the U.S. Treasury Department blacklisted six individuals and two entities that serve as the backbone for a massive, global deception. These operatives are part of a shadow workforce that siphoned nearly $800 million in 2024 alone to fund North Korea’s weapons of mass destruction (WMD) and ballistic missile programs. By using stolen identities and sophisticated front companies, these IT teams have turned the global remote work trend into a direct pipeline for sanctioned military hardware.
This is not just a case of simple fraud. It is a systematic, state-sponsored campaign that infiltrates the very heart of the Western tech economy. If you enjoyed this article, you might want to look at: this related article.
The Ghost in the Human Resources Machine
The scheme is brutally efficient. North Korean IT workers, often based in China, Russia, or Southeast Asia, assume the identities of real people—often choosing nationalities like Ukrainian to explain away accents or odd working hours. They apply for high-paying remote positions at American and European firms through popular freelance platforms. Once hired, they perform enough work to keep the paychecks coming while funneling the vast majority of their earnings back to the regime in Pyongyang.
The latest Treasury action targets Amnokgang Technology Development Company, a North Korean firm that manages these overseas delegations. It also hits Quangvietdnbg International Services Company, a Vietnam-based front. Nguyen Quang Viet, the CEO of the Vietnamese firm, reportedly converted roughly $2.5 million into cryptocurrency for the regime over a two-year period. This highlights the dual nature of the threat: these workers are not just earning a salary; they are moving capital through a web of digital assets designed to bypass the traditional banking system. For another perspective on this development, see the latest coverage from Mashable.
Beyond the Paycheck
The financial theft is only the first layer. Investigative findings show that these "workers" often act as trojan horses. In several documented cases, once a North Korean operative gained access to a company’s internal network, they installed malware to exfiltrate proprietary data or plant ransomware.
Consider the case of Yun Song Guk, a North Korean national based in Boten, Laos. Yun managed a team of IT workers who performed freelance tasks while coordinating dozens of financial transactions through facilitators like Hoang Minh Quang. This wasn't just a side hustle. It was a coordinated intelligence and revenue operation. When these workers are embedded in a company’s Slack, Jira, or AWS environment, the potential for catastrophic intellectual property theft is staggering. They aren't just coding; they are scouting.
The Crypto Connection and Sanctions Evasion
Cryptocurrency is the lifeblood of this operation. The Treasury’s Office of Foreign Assets Control (OFAC) frozen 21 specific wallet addresses across multiple blockchains, including Ethereum and Tron, as part of this crackdown. These wallets serve as digital waystations.
- Money Laundering: Funds are moved through cross-chain bridges and decentralized finance (DeFi) protocols to obscure their origin.
- Identity Laundering: Operatives use "proxy" individuals, like Dominican national York Louis Celestino Herrera, to open bank accounts and handle the fiat-to-crypto conversion.
- Procurement: The "clean" crypto is then used to buy specialized machinery, dual-use electronics, and other restricted components for the North Korean military.
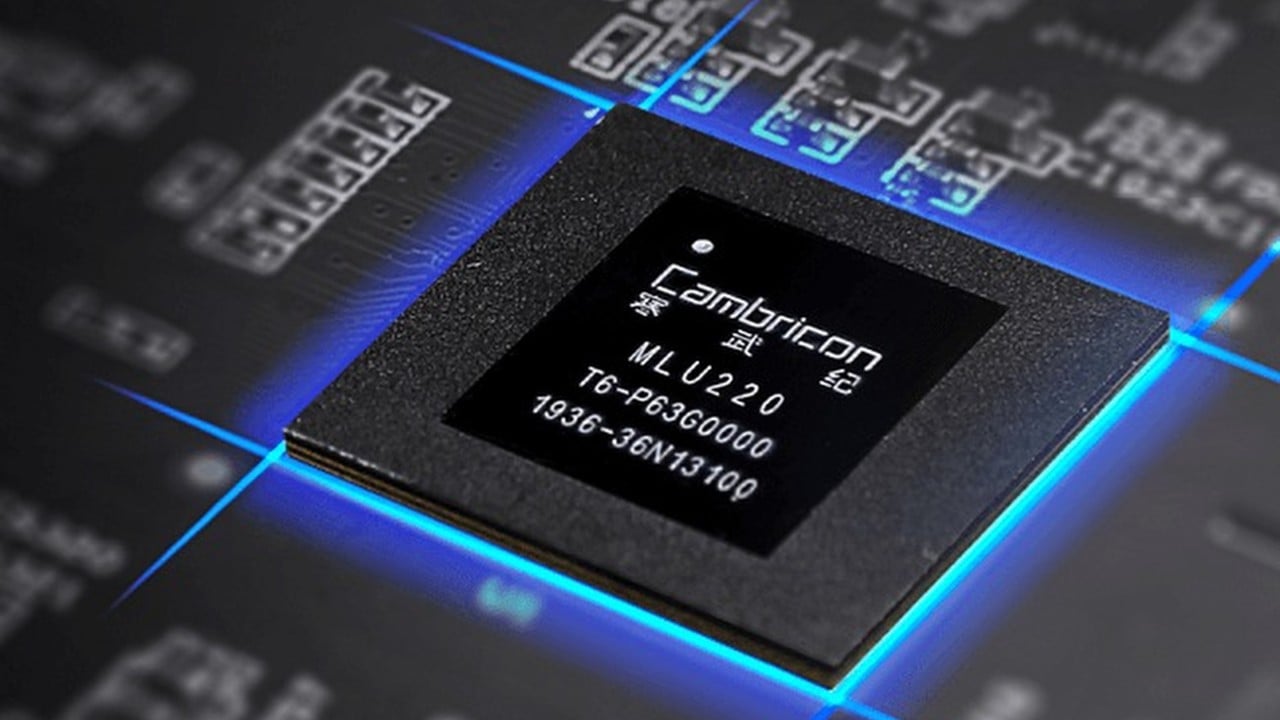
The scale is immense. While $800 million is the estimated 2024 haul from IT work, North Korean state-sponsored hackers have stolen over **$3 billion** in digital assets over the last three years. This combined war chest allows the regime to maintain a high-tech military program despite being one of the most isolated nations on Earth.
A Systemic Vulnerability
The problem lies in the friction-free nature of the modern digital economy. Companies are under pressure to hire quickly and at scale. Background checks often fail to catch sophisticated deepfakes or stolen credentials. Some North Korean workers have even been known to use AI to alter their appearance and voice during video interviews.
The reliance on Southeast Asian facilitators remains a major blind spot. While the U.S. and South Korea have stepped up coordination, countries like Laos and Vietnam still provide fertile ground for these networks to operate. The facilitators listed in the latest sanctions, such as Do Phi Khanh and Hoang Van Nguyen, acted as proxies for high-level nuclear procurement agents, proving that the distance between a "freelance developer" and a "nuclear facilitator" is shorter than most CEOs realize.
The Corporate Response
For businesses, the "trust but verify" model is broken. Standard identity verification is no longer enough when the adversary is a nation-state with a dedicated department for forgery. Companies must look for specific red flags:
- Requests to receive equipment at a residential address that differs from the home address on file.
- Consistent use of VPNs or remote desktop protocols to hide the worker's true location.
- Multiple employees sharing the same banking information or cryptocurrency payout addresses.
- Inconsistent voice or video quality that suggests the use of real-time filters or deepfake technology.
The sanctions against these six individuals and two firms are a necessary tactical strike, but they represent only a fraction of a much larger apparatus. As long as the demand for remote tech talent remains high and the barriers to digital entry remain low, the regime in Pyongyang will continue to treat the global job market as its personal ATM.
Check your payroll. Verify your access logs. The person fixing your bugs today might be the one funding a missile test tomorrow.