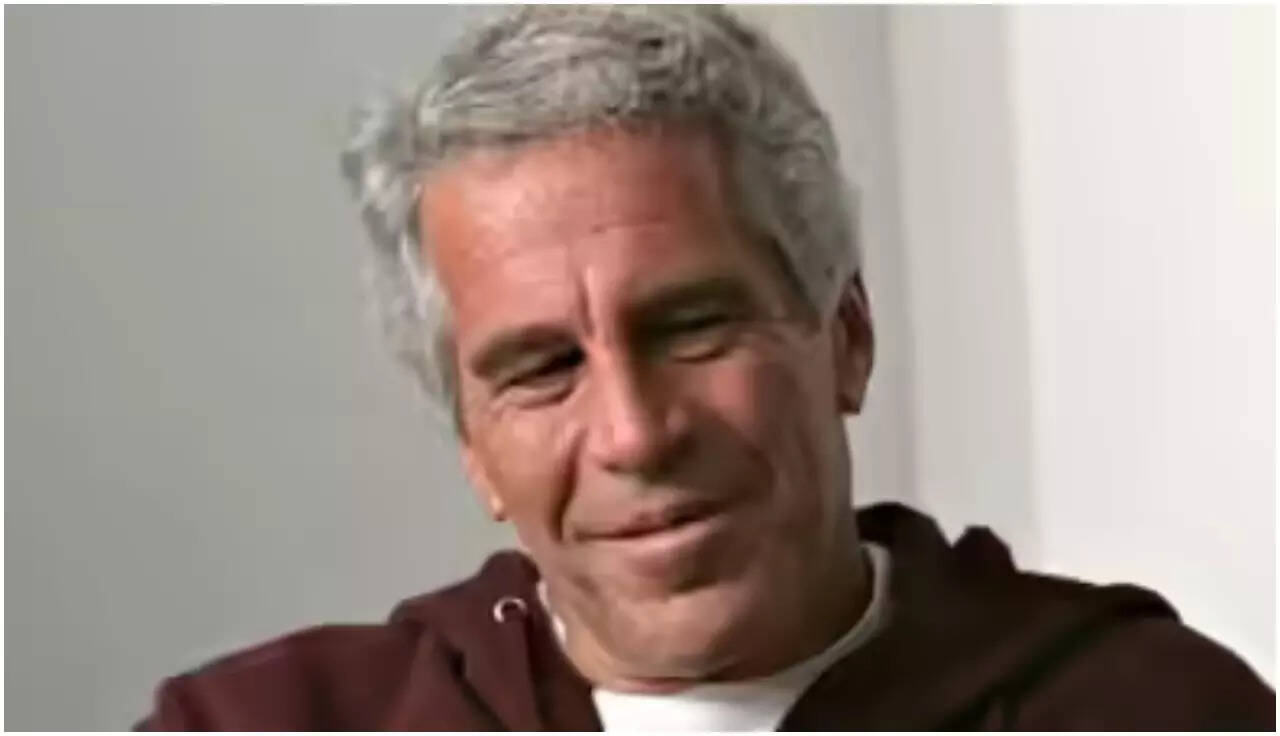
Surveillance footage documenting the hours before Jeffrey Epstein’s death at Manhattan’s Metropolitan Correctional Center (MCC) does not merely record human error; it exposes a systemic collapse of operational integrity. The video shows correctional officers Tova Noel and Michael Thomas congregating at a desk, reviewing documents, and using telephones when they were contractually and procedurally required to conduct physical checks. This footage transforms a high-profile anomaly into a case study of operational drift, where deviations from standard operating procedures (SOPs) become the accepted norm.
To analyze the failure requires looking past the surface-level negligence of two individuals and deconstructing the structural bottlenecks within the Federal Bureau of Prisons (BOP). The incident serves as a blueprint for understanding how high-security protocols disintegrate under the weight of labor shortages, fatigue, and the normalization of deviance.
The Three Pillars of Systemic Operational Collapse
An interrogation of the event reveals three distinct vectors of failure. Security protocols do not collapse because a single person forgets a task; they collapse when environmental conditions degrade the friction required to commit an error.
1. Labor Elasticity and Cognitive Depletion
Fatigue destroys executive function and situational awareness. One of the officers was working a mandatory double shift, an institutional norm within understaffed correctional facilities. When overtime becomes a structural requirement rather than a contingency measure, the institution externalizes its operational deficits onto the cognitive bandwidth of its staff.
The cognitive depletion caused by extended shifts reduces vigilance. The decision to remain at a desk rather than execute a physical patrol is a path-of-least-resistance response to acute physiological exhaustion.
2. Information Redundancy and the Attentional Blindness Loop
The Special Housing Unit (SHU) lieutenant placed bright orange physical signs on computer monitors reading, "Mandatory rounds must be conducted every 30 minutes on Epstein...". This reflects an ad-hoc attempt to override a broken system through brute-force visual cues.
In high-stress environments, operators develop attentional blindness to non-integrated warnings. If a warning is taped to a monitor rather than integrated into a digital dashboard or a biometric sign-off system, it becomes background noise. The physical removal or ignoring of this sign demonstrates that analog interventions cannot cure digital or systemic apathy.
3. Verification Asymmetry and Data Falsification
The guards were accused of falsifying logs to indicate checks had been performed when they had not. This highlights a fundamental flaw in manual auditing: the data input (the handwritten or logged check) is controlled by the same agent responsible for the physical action. Without independent verification—such as RFID scanners at the cell door, body-worn cameras, or automated timestamping—the audit trail relies entirely on the honor system.
The incentive structure in manual logging actively rewards falsification. If an officer misses a round due to fatigue, logging the miss triggers disciplinary action. Falsifying the log carries zero immediate penalty and rectifies the record, assuming no catastrophic event occurs to trigger a review.
Quantifying the Mechanism of Operational Drift
Sociologist Diane Vaughan defined "the normalization of deviance" as the process where a system’s operators gradually accept a lower standard of performance until that lower standard becomes the baseline. The MCC surveillance footage captures the terminal phase of this drift.
The progression typically follows a predictable mathematical and behavioral decay curve:
- The Baseline Friction (Time zero): The institution establishes a strict rule (e.g., cell checks every 30 minutes).
- The First Violation: A guard skips a check because of an immediate distraction or fatigue. No negative outcome occurs.
- The Feedback Loop: The absence of negative consequences teaches the operator that the rule is unnecessarily conservative. The perceived risk of skipping a check drops.
- The New Equilibrium: Skipping checks becomes standard behavior. The system appears stable until an outlier event (the suicide of a high-profile inmate) occurs.
The surveillance footage shows the guards casually milling about precisely because they believed they were operating within a normal, low-risk shift. They were not behaving like conspirators; they were behaving like bored employees in a system where cutting corners had never previously resulted in a crisis.
Auditing the Blind Spots of the Bureau of Prisons
The Department of Justice (DOJ) investigation into the MCC revealed a culture where procedural shortcuts were tolerated because the facility was chronically understaffed. Assessing the facility’s vulnerability requires measuring the gap between administrative expectations and physical capacity.
Structural Deficits in Inmate Supervision
The directive stated that Epstein required a cellmate ("bunkie") at all times and was fresh off suicide watch. Transferring an inmate off suicide watch into a standard SHU cell without a cellmate immediately concentrates the risk of self-harm.
When the system removed the internal control mechanism (the cellmate), it placed 100% of the risk mitigation on the 30-minute guard patrols. When the guards failed to execute those patrols, the system was left with zero layers of defense. Effective risk management requires the Swiss Cheese Model of accident causation, where multiple overlapping layers of defense prevent a single point of failure. By removing the cellmate and failing the patrols, all the holes in the cheese aligned.
The Economic Cost of Manual Surveillance
The reliance on human physical patrols represents a high-cost, low-reliability model of surveillance. Human attention is expensive, degrades over time, and is subject to emotional and physical variance.
Modern high-containment environments utilize tiered technology to eliminate human variability:
- Passive Biometric Monitoring: Pressure sensors in bedding or thermal imaging to detect movement and heart rates without invading privacy.
- Electronic Checkpoints (Guard Tour Systems): Requiring guards to scan a physical fob at the cell door to verify proximity and duration.
- Computer Vision Auditing: Using artificial intelligence to scan surveillance feeds in real-time, alerting external supervisors if a patrol has not crossed a specific camera's field of view within the designated timeframe.
The MCC lacked these basic technological failsafes, relying instead on paper logs and neon sticky notes.
Tactical Reconstitution of High-Security Protocols
Fixing institutional failure requires moving beyond assigning individual blame. Firing two guards does not fix the architectural problem that allowed them to sit idle. To prevent systemic operational collapse, high-containment facilities must execute a structural overhaul of their operating models.
Step 1: Decentralize the Audit Mechanism
The entity performing the check must not be the entity that verifies the check.
- Implement biometric or RFID scans at the cell door.
- Transmit this data to an external, off-site monitoring center in real-time.
- If a scan is missed by more than five minutes, trigger an automated alert to an external shift commander. This removes the ability of on-site personnel to cover for missed rounds.
Step 2: Flatten the Staffing Elasticity Curve
Overtime must be capped. If a facility requires mandatory double shifts to operate, it is mathematically insolvent. Operating a prison on overtime creates a negative feedback loop where exhausted guards make mistakes, face discipline, quit, and increase the overtime burden on the remaining staff. The solution is aggressive base-pay restructuring to attract a permanent, rested labor pool.
Step 3: Hard-Code Constraints into Housing Software
The system allowed Epstein to be housed without a cellmate despite an active directive. A modern facility management database must have hard-coded logic constraints. If a prisoner's risk profile dictates they need a cellmate, the database should block the transfer of the current cellmate out of the unit until a replacement is logged. The software should physically prevent administrators from creating a single-occupancy variable for high-risk profiles.
The Strategic Liability of Inertia
The constraints of these recommendations are economic and cultural. Upgrading to automated, off-site verified surveillance systems requires capital expenditure that public prison budgets frequently lack. Furthermore, unions and legacy staff often resist granular tracking systems (like RFID fobs) because they strip away operational autonomy.
The surveillance footage from the MCC stands as visual data proving that human autonomy, when subjected to fatigue and systemic neglect, degrades into liability. True operational security is achieved not when employees promise to follow the rules, but when the system is designed to make breaking the rules impossible. Moving forward, the mandate for correctional and high-security institutions is to shift from a culture of trust-and-verify to a culture of hard-coded, automated architectural constraints. Institutions that fail to execute this shift will remain vulnerable to the laws of entropy and operational drift.